What Security Responsibilities Your Business Owns and What Your Cloud Provider Doesn’t
With more and more businesses migrating to the cloud, service providers like AWS, Azure and Google offer a critical services for global businesses which can allow you to scale and pivot, adding additional services and storage as an when you require, avoiding heavy upfront hardware and maintenance costs which most businesses simply can’t afford. The cloud offers quick deployment, easy management and maintenance and and commercially viable solution for most and we love it!
But a common misconception trips many up. This assumption is that often businesses assume the provider handles all security within the cloud. “I pay for Microsoft 365 Office Premium so I am protected as much as I need to be” (a common response we hear all the time) which simply isn’t the case.
At DataFortified, we see and hear this daily – teams over-relying on providers while overlooking their own duties. So, here is what the shared responsibility model actually means and will clearly indicate who owns what.
In simple terms: Cloud providers provide a secure platform of which they maintain. Everything you put on that platform such as files, users, configurations and third party applications are your responsibility.
Let's break it down
Whether you choose to go with Microsoft, AWS or Google you will be provided with an enterprise-grade, highly fortified platform in which will enable you to effectively and efficiently, operate and manage your business. With many businesses making a partial or full move to the cloud, this is very common and the providers listed are the industry gold-standard.
But remember, beyond the infrastructure you are buying – everything you put on it – files, users – the lot – is your responsibility and any loss of this information is your responsibility also and NOT the service providers.
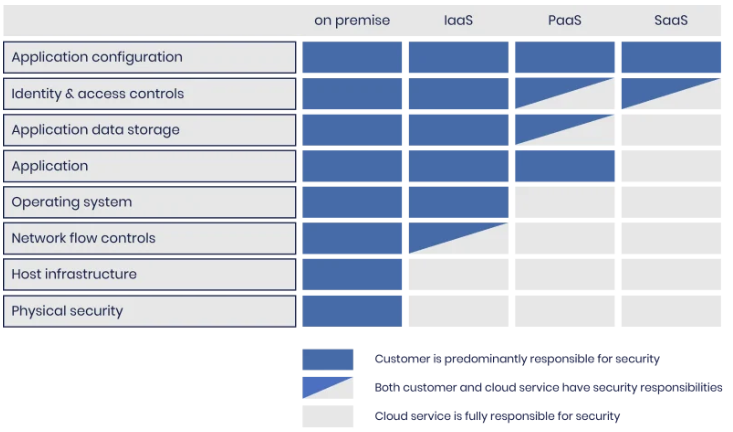
The table below breaks down the responsibility allocation options for the four main deployment strategies. It shows which service components the customer and the cloud provider is responsible for (across IaaS, PaaS and SaaS deployment models) and is courtesy of The NCSC.
Clearing up the Microsoft 365 myth
Let’s clear this up once and for all. Paying for premium tiers like Microsoft 365 gives you strong baseline tools – such as MFA prompts, encryption defaults, admin dashboards etc, but you decide who gets admin rights, who can view what emails and what files, who can change and delete documents and how your overall business is seen, managed and accessed.
It is also important to note that if you get caught short the provider cannot un-do and fix a set-up you as the admin have instated or not administered correctly nor can they recover data which has been lost or deleted if no backup is in place.
At DataFortified we are experts in cloud set-ups and specialise in Microsoft 365. Find out more about our backup and archiving service for M365

The bottom line
In todays threat landscape and ultra-connected digital world where on-click can destroy everything you have spent a decade or more building, businesses can’t afford to simply guess at configurations or hope MFA just works out the box. You need a specialist partner who understands both business and security to help you get things set up correctly from the get-go and someone who you can lean on for support and to help you navigate this often daunting and highly volatile sector.
At DataFortified, we can step in as that trusted managed service provider where we will handle the heavy lifting, ensuring the jobs you need to be delegated get done.
We will help you with:
Full cloud audits mapping your exact AWS, Azure or Google Cloud responsibilities.
24/7 SOC/XDR monitoring spotting threats before they hit.
vPenTesting + configurations locking down M365, S3 buckets, and beyond.
Team awareness training. Whether it be face-to-face or platform-delivered – so your staff and team know what their responsibilities are and what is expected of them.
Compliance made simple. GDPR, ISO 27001, NIS2 evidence packs ready to go.
Are you ready to fortify your defences ? Book a free, no-obligation security review at datafortified.com or DM us today.
DataFortified: Enterprise-grade cybersecurity for UK SMBs.
#CyberSecurity #SME #UKBusiness #CloudSharedResponsibility
If you are a business and require cybersecurity services or assistance, visit our website and request a free consultation. Our experts are on hand to assist you 7 days a week – 24/7.
Disclaimer: The content provided in this blog is for general informational purposes only and does not constitute professional cybersecurity advice or a substitute for formal consultation with qualified experts. While DataFortified takes reasonable steps to ensure accuracy and timeliness, cybersecurity threats and best practices are constantly evolving and may change without notice. Use of the information is at your own risk.
By accessing this blog, you acknowledge that DataFortified, its affiliates, employees, and agents disclaim all liability for any direct, indirect, incidental, consequential, or punitive damages arising from reliance on or use of this content. For comprehensive advice and tailored solutions, please refer to DataFortified’s official business terms and conditions and privacy agreement and consult with authorised cybersecurity professionals.
Your use of this blog constitutes acceptance of these terms and does not alter or replace any contractual obligations under DataFortified’s formal agreements.